Cryptainer Enterprise meets HIPAA Privacy and Security Criteria
What is HIPAA?
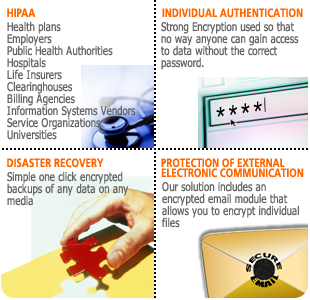
The Health Insurance Portability and Accountability Act of 1996 has brought information security to the forefront for healthcare organizations. Sometimes dubbed the Y2K of health care, HIPAA imposes sweeping standards for the privacy and protection of all electronic health information that can be linked to individuals.
Health and Human Services (HHS) is publishing final HIPAA regulations that affect virtually every area of health- related organizations in the United States, from the one-physician office to multi-entity health systems, HMOs, health care support services, and others.
A large part of this act is focused on the secure storage and transmission of confidential patient data over computer networks.
Privacy regulations were released in December 2000. They were made final on April 14, 2001, and will go into effect two years after that, in April 2003 and security regulations have to be met by April 21, 2005.
Click here to download the Cryptainer Enterprise product brochure (PDF).
Please contact us if you wish to evaluate Cryptainer Enterprise or have any commercial inquiries.
* Download Cryptainer Lite, a miniature version of Cryptainer Enterprise.
Free DownloadCryptainer Enterprise meets the Required Criteria of HIPAA Privacy and Security Regulations. Additionally, it confirms to the addressable requirements.
Be up and running in 5 minutes.
Volume sizes to 50 Gigabytes.
Works with all popular applications.
Looks and works like another hard drive.
Lightning fast!
Uses Blowfish and AES encryption algorithm
Encryption key strengths of 448 bits in blowfish and 256 bit for AES.
Administrative recovery using public/private keys.
Easy to Use, Nothing to Learn!
No knowledge of encryption required.
No need to change your working habits.
No need to remember anything but your password.
Non-compliance of these regulations will carry stiff civil and criminal penalties.
Privacy and security are inextricably linked. You can't ensure the privacy of patient information without security controls in place. In order to fully comply with the Privacy Rule, organizations will need to understand and implement a number of requirements outlined in the Security Rule. Thus it makes good business sense to consider these standards together as you consider measures for HIPAA compliance. Covered entities that take the appropriate steps now to address both of these regulations will benefit not only from compliance with HIPAA but will experience a return on investment by moving business process on-line.
Most companies invest millions of dollars in putting up firewalls and trying to secure their networks. Ironically they spend the least amount of money in protecting the area where the data actually resides or is created-the PC's employees use The cost involved in securing data at the user level is minimum and its criticality maximum. Encryption renders your data, even if accessed by an unauthorized person,unintelligible and unusable. By adopting encryption you can ensure complete security and privacy of your data.
Our flexible, end-user dependent electronic security and privacy solutions conform to the HIPAA guidelines and provide complete solutions to the healthcare institutions electronic security requirements. Most end users of HIPAA compliant electronic security products may not be conversant with electronic security requirements and concepts.
164.530(c)(1) Standard: Safeguards. A covered entity must have in place appropriate administrative, technical, and physical safeguards to protect the privacy of protected health information.
164.530(c)(2) Implementation specification: Safeguards. A covered entity must reasonably safeguard protected health information from any intentional or unintentional use or disclosure that is in violation of the standards, implementation specifications or other requirements of this subpart.
| Standards | Sections Implementation | Specifications | Compliance | Cryptainer Enterprise |
|---|---|---|---|---|
| Access Control | 164.312(a)(1) |
Unique User Identification Emergency Access Procedure Encryption and Decryption |
Required Required Addressable |
Meets Meets Meets |
| Audit Controls | 164.312(b) | Required | Meets | |
| Person or Entity Authentication | 164.312(d) | Unique User Identification | Required | Meets |
| Transmission Security | 164.312(e)(1) | Encryption | Addressable | Meets |
The HIPAA Security Rule specifically focuses on the safeguarding of electronic protected health information (EPHI). Although FISMA applies to all federal agencies and all information types, only a subset of agencies is subject to the HIPAA Security Rule based on their functions and use of EPHI. All HIPAA covered entities, which include some federal agencies, must comply with the Security Rule. The Security Rule specifically focuses on protecting the confidentiality, integrity, and availability of EPHI, as defined in the Security Rule. The EPHI that a covered entity creates, receives, maintains, or transmits must be protected against reasonably anticipated threats, hazards, and impermissible uses and/or disclosures.
Resource Guide for Implementing the HIPAA Security Rule as published in National Institute of Standards and Technology (NIST). Download in PDF Format.
Health and Human Services (HHS) proposes to amend or renumber existing rules that relate to compliance with, and enforcement of, the Administrative Simplification regulations (HIPAA rules) adopted by the Secretary of Health and Human Services (Secretary) under subtitle F of Title II of HIPAA (HIPAA provisions). These rules are codified at 45 CFR part 160, subparts C and E. In addition, this proposed rule would add a new subpart D to part 160. The new subpart D would contain additional rules relating to the imposition by the Secretary of civil money penalties on covered entities that violate the HIPAA rules. The full set of rules that will ultimately be codified at subparts C, D, and E of 45 CFR part 160 is collectively referred to in this proposed rule as the "Enforcement Rule." Finally, HHS proposes conforming changes to subpart A of part 160 and subpart E of part 164. The statutory and regulatory background of the proposed rule is set out below. A description of HHS's approach to enforcement of the HIPAA provisions and the HIPAA rules in general, the approach of this proposed rule in particular, and each section of the proposed rule follows. The preamble concludes with HHS's analyses of impact and other issues under applicable law.
45 CFR Parts 160 and 164 HIPAA Administrative Simplification; Enforcement; Proposed Rule as published in the Federal Register. Download in PDF Format.
| Point of Comparison | Other HIPAA Solution | Cryptainer Enterprise |
|---|---|---|
| Cost to enter | High | Low |
| Cost to maintain | Very High | Low |
| Cost to upgrade | Very High | Low |
| Total Cost of Ownership | Very High | Moderate |
| Return On Investment | Low | Very High |
| Expertise Required | High | Low |
| Ease of Implementation | Very Low | High |
| Timeframes | High | Low |
| Success Rate | Moderate | 100% |
Click here to download the Cryptainer Enterprise product brochure (PDF).
If you wish to evaluate Cryptainer Enterprise or have commercial inquiries, please contact us.